Google Maps will provide the most efficient route based on the fuel of each vehicle
22/07/2022The latest update of the Google Maps beta, version 11.39, would allow users to choose between different vehicle options, gas, diesel, electric and hybrid, and based on these choice, the application will propose the route that allows the driver to save more into fuel or power. This novelty is collected by the specialized Google portal, 9to5Google, which has had access to the update that would still be in the testing phase. The new option would come to complete others already planned, such the one tha allows Google Maps to indicate the least polluting routes to users, as long the option for that itinerary does not imply a substantial change in time behind the wheel, in relation to the fastest route.
[ ... ]49% of consumers are willing to favor brands that explain data usage in AI interactions
17/04/2024Artificial intelligence (AI) has become a fundamental tool for companies striving to provide personalized and efficient customer interactions. However, a new report reveals that the lack of transparency in data usage by brands is affecting consumer trust. According to Twilio's fifth 'State of Consumer Engagement Report', based on a global survey including over 4,750 B2C executives and 6,300 consumers across 18 countries, 49% of consumers would trust a brand more if it disclosed how it uses data from AI-driven interactions. The report also highlights that, although 91% of brands claim to be transparent with their customers about AI usage, only 48% of consumers agree. In this context, data protection emerges as a priority for consumers, with six out of ten indicating it's the best way for brands to earn their trust. This data security concern is shared by, the 40% businesses globally that considerate important to find a balance between security and customer experience as one of their most pressing challenges. AI-driven customer experience for brands AI-driven personalization is a key strategy to enhance customer relations. The report points out that companies adopting personalization experience a significant increase in consumer spending, averaging 54% more compared to those that don't. AI not only helps bridge the customer experience gap but also provides additional benefits, such as better data-driven decision-making and increased customer satisfaction. However, the report highlights that many companies face difficulties in activating customer data. Globally, only 16% of brands fully agree that they have the necessary data to understand their customers.
[ ... ]Cisco
CiscoCisco creates powerful connections and high-end protection systems throughout the world. Founded by computer specialists in 1984 at the National Center for Engineering Pathways to Innovation located on the campus of Stanford University, its first achievement was to connect computers between the different departments of the University itself, creating the first efficient and practical connectivity network. Today, it is one of the leading companies in Internet communications, enabling people to establish powerful connections in business, education, research, and creative sectors. It is headquartered in San Jose, California, with subsidiaries around the world.
[ ... ]Cables
To connect our computers to the network, link them to each other or link them to other peripherals, it is essential to have the right cable for each type of connection. The difference between using a correct cable or resorting to any of the many that we store in the "cable drawer", can range from a lower performance of the Internet connection to failures in screen resolutions, sound deficiencies, failures in data storage ... or even the loss of information or inoperability of the equipment. Find here the cable you need, with all its specifications and precise details to make your choice the right one.
[ ... ]
SSD laptops
SSD laptops are the ultimate solution to laptop slowness and inefficiency. With an SSD laptop, you will no longer have to wait forever for the operating system to start up, you will eliminate the lag in opening and saving documents, and you will be able to open programs and applications almost immediately. Choose the SSD laptop configuration that suits you best. You'll find gaming and 2-in-1 laptops, ultrabooks, workstations, and more - the choice is yours!
[ ... ]WiFi Security: Assessment of threats in wireless networks
08/03/2024Wifi connectivity has gone from being limited to restricted environments to becoming omnipresent in virtually every aspect of our daily lives. The ability to connect to the Internet from anywhere, be it at home, in a café, at work, in public spaces, or even in-flight, has enhanced the convenience in our daily lives. Moreover, the expansion of Wifi networks and the use of new manufacturing technologies now allow the interconnection of devices, leading to the significant rise of the Internet of Things (IoT) and providing users with more comprehensive control over their digital environments. However, this proliferation of Wifi networks has also given rise to new threats that require careful evaluation and effective security strategies to ensure secure and risk-free Wifi connections for our data and information. Common Wifi security threats include data interception Man-in-the-Middle (MITM) attacks One of the fundamental challenges in Wifi security is preventing MITM attacks, where an intruder inserts themselves into the communication between two parties, compromising the integrity and confidentiality of sensitive data such as passwords and financial information. Spoofing of access points Hackers can create fake Wifi networks that mimic legitimate ones to attract unsuspecting users. Once connected to these malicious networks, our data can be captured by cybercriminals who may sell or misuse it for illicit purposes. Tips for achieving a secure Wifi connection: Strengthen authentication and use security protocols Prioritize strong encryption for networks to protect confidential information transmitted through it. WPA (Wifi Protected Access) encryption uses stronger algorithms than its predecessor, WEP (Wired Equivalent Privacy), making it more difficult for hackers to intercept and decipher data. Advanced security protocols like WPA3 provide individualized data encryption and advanced two-factor authentication (2FA) methods, adding an extra layer of security by requiring additional verification. Device management Properly manage and monitor devices connected to Wifi networks to minimize risks associated with the large number of connected devices in homes and businesses. Regularly update the router firmware and all connected devices to address potential vulnerabilities. Segmentation of the network to separate critical devices from less secure ones also helps mitigate the risk of threat propagation. Secure Router Configuration The router secure configuration is what will ensure the robustness and overall security of a wireless network. The router, being the first point of contact for devices connected to the Internet, acts as the first line of defence against potential attacks. For this reason, it is important to understand that the proper configuration of the router not only guarantees a stable and efficient connection but also establishes a protected environment that safeguards the integrity and privacy of our data. How to configure the router securely? To ensure a correct and secure configuration of the router, it is recommended to: Change the default username and password of the router, as these are easily accessible to attackers. Use strong passwords containing a combination of letters, numbers, and special characters. Disable remote administration to prevent cybercriminals from accessing the router externally. Enable WPA2 or WPA3 encryption instead of the outdated WEP for enhanced network security. Optionally, disable SSID broadcast to make the network less visible and harder to detect by hackers. Keep the router firmware updated to address vulnerabilities and improve overall device security. By following these steps, you will strengthen the security of your wireless network and reduce the chances of experiencing unwanted attacks or intrusions.
[ ... ]D-Link
D-LinkD-Link is today one of the world leaders in innovative and efficient connectivity products and systems. Their field of action is so extensive that they manufacture products for homes, businesses (small, medium, and large), and demanding service providers. For enterprises, D-Link is the only supplier able to offer unified solutions. It has extensive product ranges in areas like security and storage, switching, and IP video surveillance. In the home products market, D-Link is one of the most popular manufacturers because of its Fiber/ADSL/Cable Routing, Wi-Fi AC, Powerline, Wi-Fi Amplifiers, 3G/4G Mobility, Storage, Connectivity, Home Automation, and Video Surveillance lines. In our online store, you will see many of these products at the best price.
[ ... ]Orange transforms the gaming experience with AI and the 5G+ Stand Alone Network
29/02/2024Orange has harnessed the power of Artificial Intelligence (AI) and the advanced architecture of the 5G+ Stand Alone network, leveraging its fragmentation capabilities, to reinvent a Virtual Reality (VR) athletics video game from the 1980s. In this revamped version, users have the opportunity to become exceptionally realistic avatars, competing with other players located in various places. The game employs Artificial Intelligence (AI) to accurately identify the user's anatomy and textures, creating the avatar. This process involves a three-dimensional volumetric scan of the subject, performed with a total of 21 cameras. Based on this detailed information, the avatar is created, allowing the player to participate in thrilling athletics races, competing against virtual opponents physically located in different locations. Fragmentation technology for efficient virtual networks During the game's usage, it leverages the capacity of network fragmentation technology to establish various virtual networks on the same physical infrastructure. This is achieved through efficient resource allocation tailored to the specific needs of the service, considering key aspects such as quality, availability, privacy, and security. In the case of Orange's VR game, it achieves this by prioritizing a fast and secure connection with minimal latency for an enhanced gaming experience. Immersive Now by Orange The presentation of Orange's athletics game took place at the Mobile World Congress in Barcelona, where the orange mobile telecommunications operator also showcased a virtual reproduction of its booth using the Immersive Now 360 platform for entertainment and events.
[ ... ]Devolo
DevoloThe one thing that defines the German technology company Devolo is its commitment to bringing functional and efficient solutions to the smart grid industry. Since its founding in 2002, Devolo has been striving to give shape to the power grid of the future. This company offers communications devices for the industrial and home sector and manufactures high-performance, digitized, and user-friendly products for smart homes. Devolo is undoubtedly a driving force of innovation in digitization.
[ ... ]What is Bitcoin Halving and how does it affect the cryptocurrency?
25/02/2024The term "Halving" in the context of Bitcoin refers to a scheduled event in the cryptocurrency protocol, in which the reward for mining blocks is reduced by half. This event occurs approximately every four years and has a significant impact on the supply and demand of Bitcoin. During Halving, the number of new Bitcoins created per block is halved. This implies a decrease in the issuance rate of the cryptocurrency, which in turn can have an effect on the price and volatility of Bitcoin. Many analysts and experts are speculating about the long-term implications of the Halving and its influence on the cryptocurrency markets. Services related to Bitcoin Halving There are various types of services and tools related to Bitcoin Halving that can be beneficial for different actors in the cryptocurrency ecosystem. These services include: 1. Halving analysis and forecast This type of service provides detailed information about the past, present and future of the Bitcoin Halving. Through analysis and forecasting, it helps investors and cryptocurrency enthusiasts make informed decisions on how to position themselves before and after the event. 2. Bitcoin Mining As the reward in Bitcoin decreases, mining this cryptocurrency becomes more challenging. Bitcoin mining services offer solutions and advice to maximize mining efficiency and profitability, even in a low reward environment. 3. Financial advice related to Halving As the issuance rate of Bitcoin slows, investors may need to adapt their investment strategies. Financial advisory services specialized in cryptocurrencies and Bitcoin provide personalized recommendations and analysis to optimize investment performance in this context. 4. Development of tools for cryptocurrencies The Bitcoin Halving may generate changes in the cryptocurrency ecosystem, which may require the creation of new tools and solutions. Companies specialized in software development and applications related to cryptocurrencies can provide development and consulting services to adapt to these new demands. Bitcoin: Reward Reduction and Its Implications on the Cryptocurrency Ecosystem Bitcoin, the most famous and valuable cryptocurrency in the world, has periodically experienced an event known as a "reward reduction" or "Halving", which has significant implications on the cryptocurrency ecosystem. In this article, we will explore in depth what Bitcoin reward reduction is and how it affects both miners and investors. What is Bitcoin reward reduction? Bitcoin reward reduction is a scheduled event integrated into the cryptocurrency protocol. It occurs approximately every four years and consists of a halving of the reward miners receive for validating transactions and adding new blocks to the Bitcoin blockchain. Originally, when Bitcoin was launched in 2009, miners received a reward of 50 Bitcoins for each block mined. However, due to the reward reduction process, this amount has decreased over time. In 2012, it was reduced to 25 Bitcoins per block, in 2016 to 12.5 Bitcoins per block, and in 2020 it was reduced again to 6.25 Bitcoins per block. Implications for Bitcoin miners Bitcoin's reward reduction has a significant impact on mining the cryptocurrency. With each reduction, miners receive fewer Bitcoins for their work, which means less direct monetary reward. This may result in some miners leaving the Bitcoin network, especially those with higher electricity and mining equipment costs. On the other hand, those miners who manage to adapt and remain profitable even with a lower reward are rewarded with a larger share of the Bitcoin supply generated through mining. This concentration of Bitcoins in the hands of fewer miners can have effects on the decentralization and security of the network, since the number of active participants in the transaction validation process is reduced. Implications for investors and the price of Bitcoin Bitcoin's reward reduction also has implications for the price and supply of the cryptocurrency. As the issuance of new Bitcoins decreases, the supply in the market reduces. This may lead to higher relative demand if Bitcoin demand continues to grow or remains stable. In previous reward reduction events, a long-term increase in Bitcoin price has been observed. This is because the decrease in the supply of new Bitcoins can lead to greater perceived scarcity and therefore an increase in their value. However, it is important to note that the price of Bitcoin is highly volatile and can be influenced by a variety of external factors, so a continued increase after reward reduction cannot be guaranteed. Bitcoin's reward reduction is a key event in the life of the cryptocurrency and has implications for both miners and investors. As the number of new Bitcoins generated is halved, miners must adapt to remain profitable and the supply of Bitcoin on the market may decrease. However, this event can also have a positive impact on the price of Bitcoin in the long term. It is important to understand and take these factors into account when evaluating investment potential in Bitcoin and the cryptocurrency market in general. Bitcoin and limited supply: a unique combination Bitcoin has captured the attention of the financial world like no other cryptocurrency. One of its most notable features is its limited supply, meaning that only a finite number of bitcoins will be created in the world. This contrasts with traditional fiat currencies, which can be printed at the discretion of governments. How does Bitcoin limited supply work? Bitcoin was designed to have a total supply of 21 million coins. As new blocks are mined by users and added to the Bitcoin blockchain, new coins are generated and distributed as rewards to miners. However, this reward is halved in an event known as "Halving", which occurs approximately every four years. Halving ensures that the rate of issuance of new bitcoins decreases over time, following a predictable mathematical function. Currently, the reward per mined block is 6.25 bitcoins, but this number is expected to reduce further in the future. This controlled scarcity mechanism is a central part of Bitcoin's monetary policy. Advantages of Bitcoin Limited Supply Bitcoin's limited supply has several significant advantages: Sense of scarcity: The limitation in the supply of Bitcoin makes it a scarce and valuable asset. As it approaches its maximum supply, demand and price are expected to increase. Inflation Protection: Unlike fiat currencies, Bitcoin cannot be inflated or devalued at the discretion of governments. Its limited supply protects it from inflation and makes it a safe store of value. Monetary stability: With carefully controlled supply, Bitcoin offers greater monetary stability compared to national currencies, which can be affected by political and economic decisions. Challenges and debates surrounding the limited supply of Bitcoin Despite the advantages, Bitcoin's limited supply has also generated debates and challenges. Some argue that the scarcity of bitcoins could hinder its mass adoption as an everyday currency. Price volatility is also an issue of concern. Furthermore, the fact that only about 80% of all existing bitcoins have been mined raises questions about how the latest bitcoins will be distributed and how this will affect the network and its sustainability in the future. Bitcoin has revolutionized the financial world with its limited supply and unique monetary policy. Controlled and predictable scarcity is an essential part of its design, providing a solid alternative to traditional fiat currencies. Although limited supply can pose challenges and debates, it also offers significant benefits, such as a sense of scarcity, protection against inflation, and monetary stability. As Bitcoin continues to mature and its supply approaches its maximum limit, its value and relevance in the financial world continues to grow, leaving investors and enthusiasts with great anticipation about its future.
[ ... ]eero
eeroEero is an American startup that was founded in 2014, popularized for being able to create and launch to the market before any networking company, the first mesh WiFi device system in 2016. Very few companies at the time offered a better WiFi solution to consumers. They brought a novel and efficient home Wi-Fi system with high-speed performance, super secure in every room of your home, increasing the efficiency of your internet and reducing network congestion. Eero is currently and since 2017 a company owned by Amazon.
[ ... ]Chat with RTX by Nvidia: Localized customization of chatbots without Internet
19/02/2024Nvidia introduces an innovative tool in the chatbot realm called Chat with RTX, designed for the personalization of conversational assistants. Powered by generative Artificial Intelligence (AI), Chat with RTX operates locally on computers with GeForce RTX Series 30 graphics cards running Windows 10 or Windows 11. Chat with RTX and the IA revolution for chatbots This decentralized approach eliminates the reliance on an internet connection for chatbot functionality. Unlike many conventional virtual assistants, which require constant cloud connectivity for processing and generating responses, Chat with RTX operates internally on the user's device. According to Nvidia, this feature not only enhances privacy by avoiding the transmission of sensitive data over the network but also provides a quicker and more efficient response. With Chat with RTX, users can create personalized chatbots in the style of ChatGPT, Gemini or Copilot for conversational queries. This format allows the incorporation of YouTube videos, text in different formats, and URLs for contextual queries. Nvidia's tool is optimized to leverage the capabilities of computers running Windows 10 or 11 with a GeForce RTX Series 30 GPU and 8GB of video random access memory (VRAM).
[ ... ]HP
HPAnyone who is still immersed in the world of PCs today is undoubtedly familiar with the HP brand. Hewlett-Packard, founded in 1939 in the United States, is one of the pioneering brands in computer software and IT services. As a curious fact, in 1972, the company launched its first mini-computer, the HP 3000, a product line that is still in use today in many companies. That same year they launched the world's first scientific pocket calculator at an affordable price.
[ ... ]Arc Search, AI-powered search engine for iOS
05/02/2024The Browser Company has introduced its latest innovation to the market, Arc Search, a search engine exclusively designed for iOS devices that integrates artificial intelligence and private browsing functionalities. Arc Search promises seamless and interruption-free navigation, free from annoying ads. Driven by artificial intelligence, this search engine offers, also, advanced features such as the ability to summarize visited web pages and provide search results more efficiently. Additionally, it stands out for its ad blockers, a reading mode that minimizes distractions, and a keyboard designed to initiate searches with just a few taps. In addition to Arc Search, in the spring, The Browser Company will also launch its web browser ARC, based on Chromium, with the ambition to challenge the supremacy of Google Chrome. With these releases, The Browser Company has explained that it aims not only to establish itself as a robust option in the realm of browsers and search engines but also to redefine how users interact with information on their iOS devices.
[ ... ]Netgear
NetgearNetgear, founded in 1996 and headquartered in California, is a multinational computer networking company. Its specialty is the production of networking hardware and accessories to help all types of consumers, businesses, and service providers get the best and fastest possible connectivity. In other words, it helps everyone. Netgear products are designed and manufactured to make the user’s life easier and to ensure that his/her connection is of the best possible quality because no technology is valid if it is not accessible and efficient.
[ ... ]Xiaomi
XiaomiIn little more than 10 years, the Chinese multinational Xiaomi has become a giant in the electronics industry. It is a really impressive trajectory if we take into account that in this short period of time it has put itself on a par with companies like Apple, Samsung or Huawei. Xiaomi, has realized that the world is a big market, and it does not stop expanding. It is now an Internet company with smartphones and smart hardware connected by an Internet of Things (IoT) platform at its core. Its sales are growing steadily and it continues an unstoppable race to innovate and achieve a high-quality user experience and operational efficiency.
[ ... ]The Neeva search engine fails and shuts down
02/06/2023After months of efforts, Neeva, the search engine designed by two former Google employees that aimed to provide a user-tracking-free and ad-free service, has announced its closure. Since its launch, Neeva has failed to gather a sufficient user base to sustain the project, even after announcing Neeva AI and becoming the first search engine to provide real-time AI-driven answers to most queries. Therefore, today, on June 2nd, Neeva will disappear as a search engine. Its founders will redirect their business to a new area, and subscribers with active licenses will receive a refund for the unused period. Neeva has also announced the deletion of all user data.
[ ... ]Google Maps introduces new search opcions of ecological routes
21/09/2022Google will incorporate in Google Maps , new ecological routes that will be able to guarantee a lower impact from vehicles on the environment and, also, minimize fuel consumption.This new functionality of more sustainable itineraries will be implemented in Europe during next weeks, after having been successfully tested in the United States and Canada, where, according to Google in a statement sent to Europa Press, they have contributed to avoiding more than half a million tons of carbon emissions, in only one year.To suggest the best ecological route, Google Maps will ask the user about the type of engine of the vehicle that is going to use and then will show the driver all his available itinerary options and an accurate estimate of the consumption efficiency of the vehicle.Additionally, the package of new Google Maps features also incorporates the option to activate the display of charging points for electric vehicles; new bike routes, and Live View option, to supervise streets in real time.
[ ... ]Fundaci�n Telef�nica wants to convert the world's first website into a World Heritage Site
27/05/2022Fundación Telefónica is determined that the first website in history, the one of the british computer scientist Bernes-Lee, from 1990, could be declared a World Heritage Site by UNESCO and has announced a campaign to achieve this goal. The action named “ElSitio1155” identifies the Bernes-Lee website as a fundamental piece of the history and culture of humanity. And this is like this, becouse this website, in addition to be the first to exist, marked the birth of the World Wide Web, and also led to the first step to the connected world of today. If recognition is achieved, it would be the first time that UNESCO would do so to a virtual and non-geographical site as usual. Prior to the presentation of its official proposal, Fundación Telefónica has launched a support campaign through its social networks and communication channels to make everyone aware of the importance of this first website in the world, the pioneer of more than 1.9 million websites accounted for on December 31, 2021.
[ ... ]How to sign a PDF document with electronic signature?
24/06/2021When a document needs to be signed by one or more people, the usual thing, until now, has been to print it and stamp by hand the necessary signatures to validate or make its content official. This requires paper, printer, ink, but above all access to the document by all signatories, which is not always easy due to geographical location, availability, timing, etc. With teleworking on the rise and a growing globalization of business, these drawbacks have become more evident than ever, although they have found a quick and effective solution in electronic signatures. What is an electronic signature for? The electronic signature is a digital validation system for documents that unequivocally identifies the signatory. The electronic signature is assimilated to the handwritten signature and therefore its digital stamping on a document gives it the same validity, as it would have had with a handwritten signature. What are the advantages of electronic signatures? Electronic signatures simplify document management processes that require the validation of documents such as pdf signatures, facilitating remote signing by one or more people regardless of where they are located, or the situation or time of day they receive them. This flexibility contributes to the efficiency and agility of this type of procedure and being a secure signature system, it is suitable and useful in many areas related to business management, administrative management, e-commerce, informed consent and many other procedures. In addition to the versatility, practicality and security of the online PDF signature, we must also point out, as a great advantage of this process, its contribution to paperless. How to sign electronically? The electronic signature is easy to implement through tools specifically designed to guarantee not only the correct validation of the cryptographic signature or signatures included in a PDF document, but also that it cannot be altered and that all the necessary signatures required by each situation can be added. Within the framework of this type of tool, the most advanced ones, in addition to being compatible with any browser and accessible from any type of device - computer, tablet, Smartphone,... -, make it easy to convert PDF any Word, Excel, JPG, PowerPoint... file for signing. They also allow users to request a verifiable digital signature, view the properties of the digital signature and send the document directly by email to the signatories and once signed, forward it to all parties to download it. In addition, to guarantee the privacy of the documents and the security of the online signatures, these transfers are made through encrypted files with TLS encryption. Also, when we sign documents using this type of tool, they offer the option of including a LTV (Long Term Validation) time stamp that certifies the validity of the signature in the long term. For all these reasons, tools for signing PDF documents with electronic signatures are now a must for companies and businesses in all areas where process optimization, security and sustainability are a priority.
[ ... ]What can I do if my computer runs very slow?
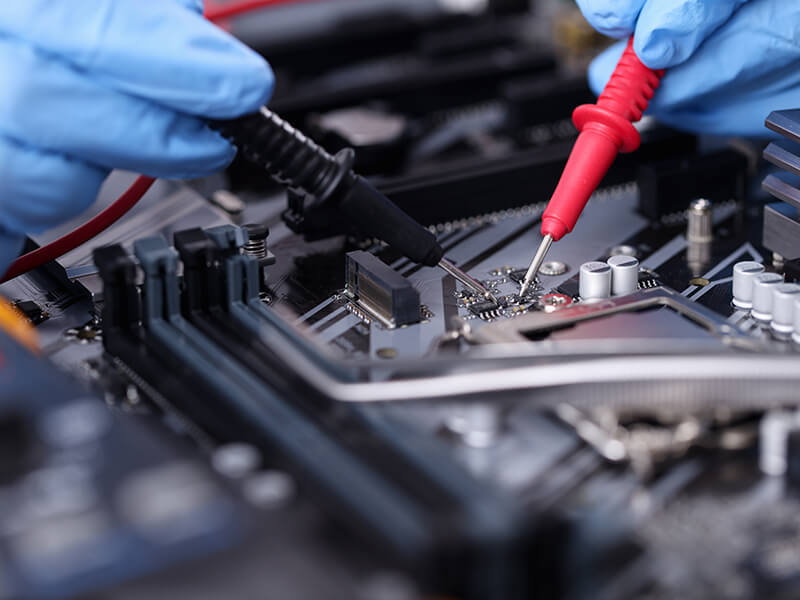
22/05/2021If your computer is running slow, do not despair. The use of a computer like any other machine needs proper maintenance and the performance of our PC can be severely affected by the lack of attention to this task. But, don't worry, if you want your computer to work as it did on the first day, we explain how to get it back. Why is my computer so slow? Computer slowness can be due to hardware, software, connectivity and even tidiness and cleanliness problems! Every computer needs a minimum maintenance so these failures can be avoided and only if we pay this kind of attention we can ensure an always-optimal performance for our computer, prolong its life and work or enjoy our PC, without despairing. I have tried everything, but my computer is still very slow. What can I do? If your computer is slow and you have already tried the typical things like closing secondary tasks, disabling the automatic execution of programs, you have verified that you have free space on the hard disk and restarted the PC, and everything is still the same, it is clear that something is wrong with your machine and you should consider resorting to a professional computer repair service, so that they can fix it. You can search a thousand videos on the Internet, but... do you really know why your computer is slow? Why does your computer start up very slowly? Or why has your computer become slow after a while of working with it? Are you sure that what you want to do will not end up causing another error or, even worse, another more serious problem? Is it necessary to go to a professional Computer Repair Service to fix the slow computer problem? The answer is yes, if what we are looking for is to really fix the problem and prevent it from happening again. You can save a lot of time and money by using a professional computer repair service. The best computer repair services work with specialized technicians who have the necessary knowledge to make a quick and accurate diagnosis that will allow you to give your computer a new lease of life. In addition, professional computer repair services have the right tools and all the licensed software to be able to intervene. What will a Computer Repair Service do to speed up my slow PC? The first and foremost thing that a professional computer maintenance service can offer you is a maintenance plan for your computer, tailored to your needs. With this alone, you will most likely avoid many problems related to the performance of your machine, including speed problems, right from the start. They will be able to, among other things, repair or replace any part of your computer causing any problem, they will perform a deep search for viruses to eliminate them; and if necessary, they can clean the cooling system of your computer to remove internal dust, one of the most common causes of slow computer performance - dust accumulated in the internal fans can reduce their efficiency and cause overheating of the machine and its mechanical components -. Sometimes we think about replacing the machine when a simple repair and a good maintenance can bring our PC back to life. When was the last time you had your computer serviced?
[ ... ]What is IT maintenance? Prevention is better than cure
19/04/2021Keeping our IT equipment in good condition is essential for the smooth running of the business. The main goal of a good IT maintenance is to ensure the proper functioning of the hardware and software of our network and IT equipment and thus contribute to the overall efficiency of our business. What is the purpose of computer maintenance services? Computer maintenance services try to anticipate failures and offer us solutions to manage our computers and computer network, optimize their operation and secure all the information contained in our machines. In case of incidents, a good computer and systems technician will solve them and also find the cause of the error to prevent it from happening again. Benefits of hiring a computer maintenance and web maintenance service Common computers, servers, hard drives, networks, connections and antivirus problems can be avoided or prevented if we carry out all their preventive maintenance needs. Advance failure detection. Incidents can occur at any time, nipping them in the bud can save us a lot of headaches throughout the life of equipment. Improve the performance and reliability of your computers and network. This ensures our software is always up to date, thus improving the efficiency, speed and machines operation and other connected equipment. Prevents data loss. Data loss can wreak havoc. Keeping the equipment in good condition reduces the chances of these accidents that are completely neutralized if, in addition, our computer maintenance services include backups and contingency and recovery plans in case of disaster. Improve our protection against cyber-attacks. Regular maintenance means that our systems have the latest and, potentially, most effective security software installed to prevent any problem with malware, viruses, spyware or other unwanted attacks. Reduce our costs. With up-to-date computers we will always maximize their useful life and minimize the risk of loss due to unplanned downtime caused by computer problems. It helps us to keep the website properly updated and backed up. The most complete IT services include additional high-value services such as web maintenance for companies and backups of the entire project so nothing is lost in case of problems. What are the functions of a computer maintenance technician? Periodic reviews of computers, equipment and networks. To ensure from day one that everything is working properly, the software is up to date and the hardware is adequate. Server management with activity monitoring. To anticipate incidents or react immediately if they occur. Backup copies. To prevent data loss both on physical equipment and in the cloud. IT security. To keep machines protected and minimize the risks of viruses, computer attacks and improper intrusions. User management. To guarantee exhaustive control of how and who can access the data stored on the company's computers and servers. Remote and on-site technical assistance. Telephone support. To ensure quick resolution for major incidents and restore the service in the shortest possible time.
[ ... ]